Evaluation
We have implemented a prototype of our design on USRP2 software
radios. We use 400 MHz daughterboards for compatibility
with the 402–405 MHz Medical Implant Communication Services
(MICS) band used by IMDs. We evaluate our prototype
shield against two modern IMDs, namely the Medtronic Virtuoso
implantable cardiac defibrillator (ICD) and the Concerto cardiac
resynchronization therapy device (CRT). Our evaluation
reveals the following:
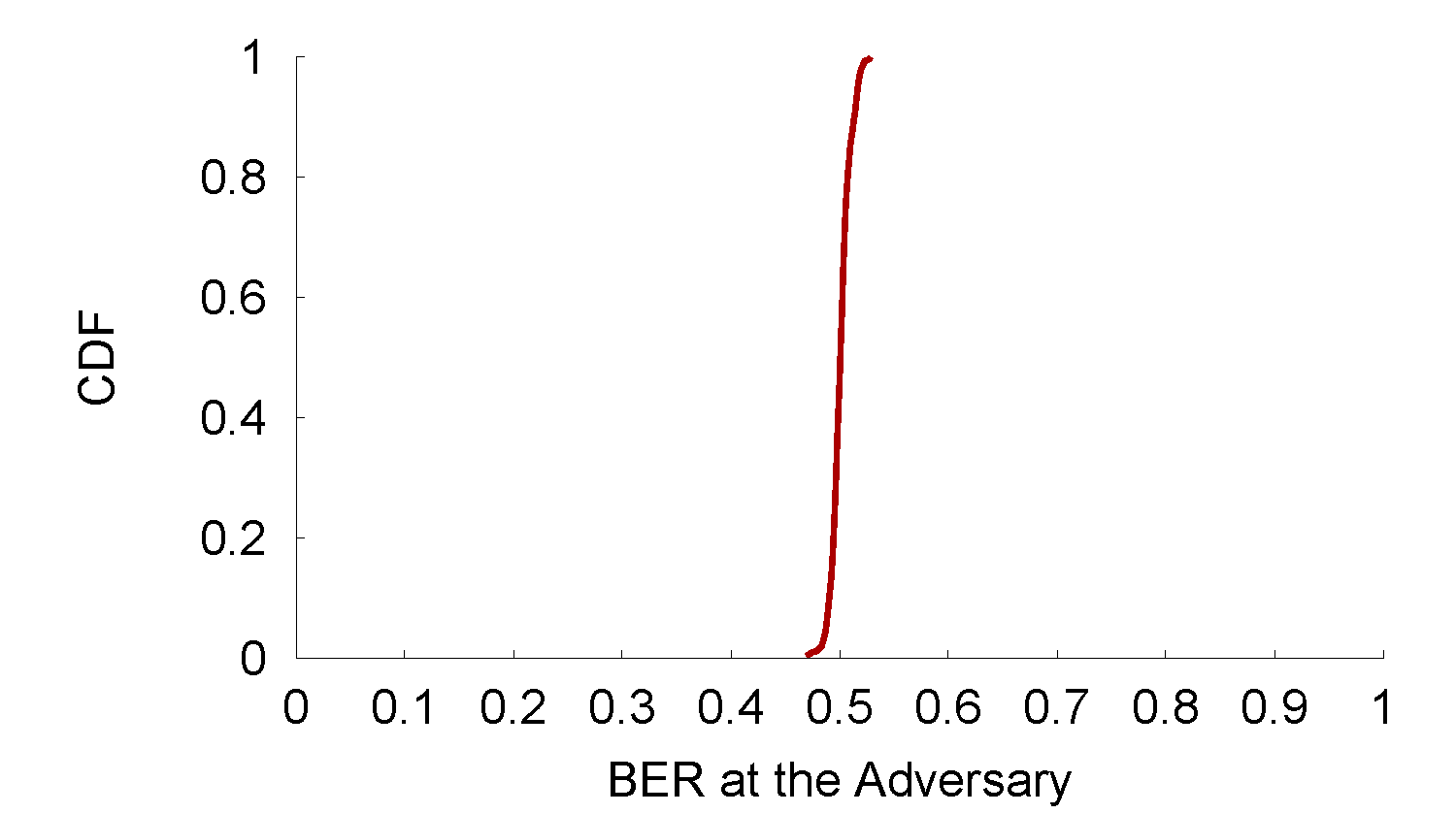
• When the shield is present, it jams the IMD’s messages, causing
even nearby (20 cm away) eavesdroppers to experience a bit error
rate of nearly 50%, which is no better than a random guess.
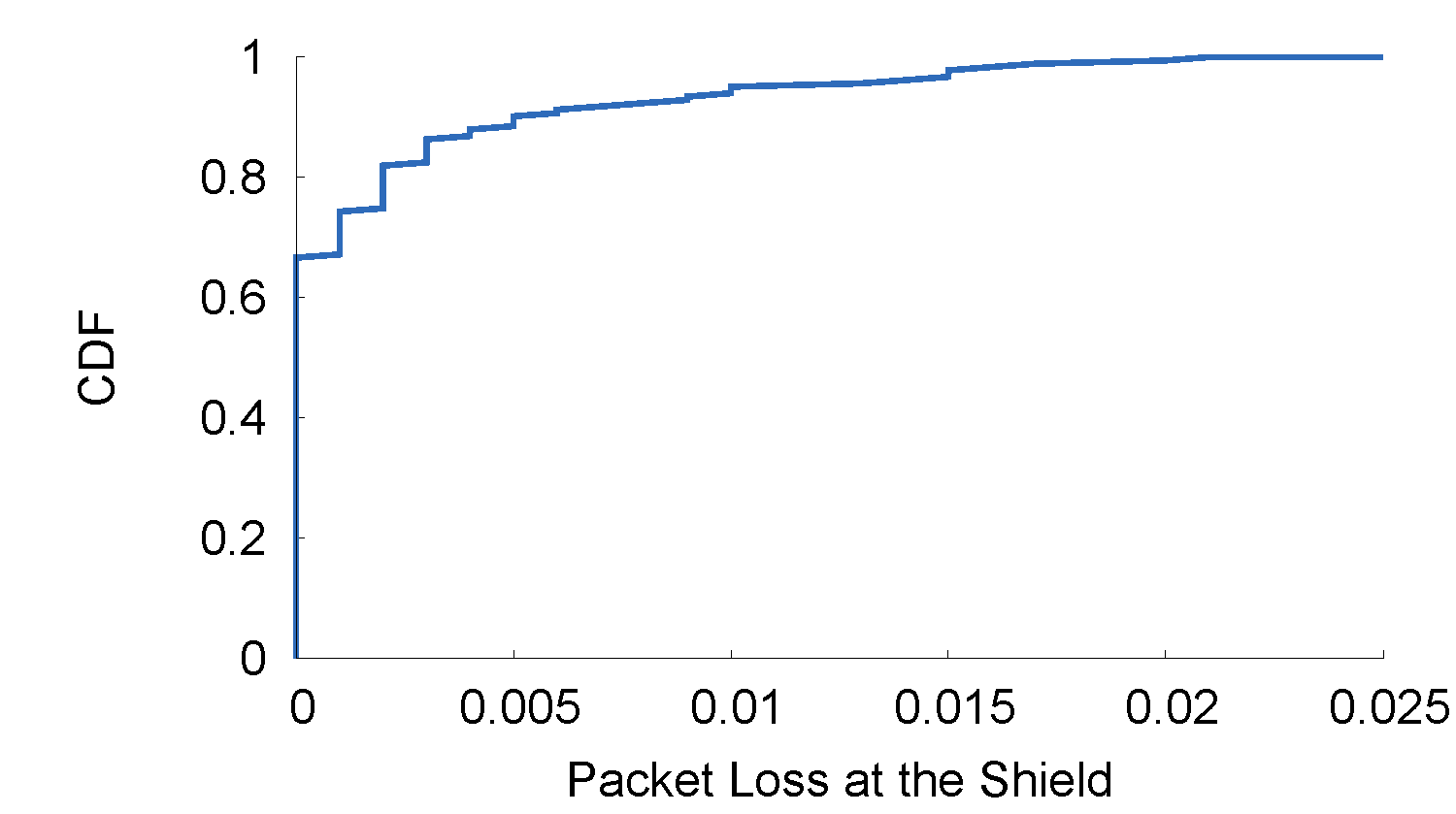
• When the shield jams the IMD’s packets, it can still reliably decode
them (the packet loss rate is 0.2%, which is negligible). We
conclude that the shield and the IMD share an information channel
that is inaccessible to other parties.
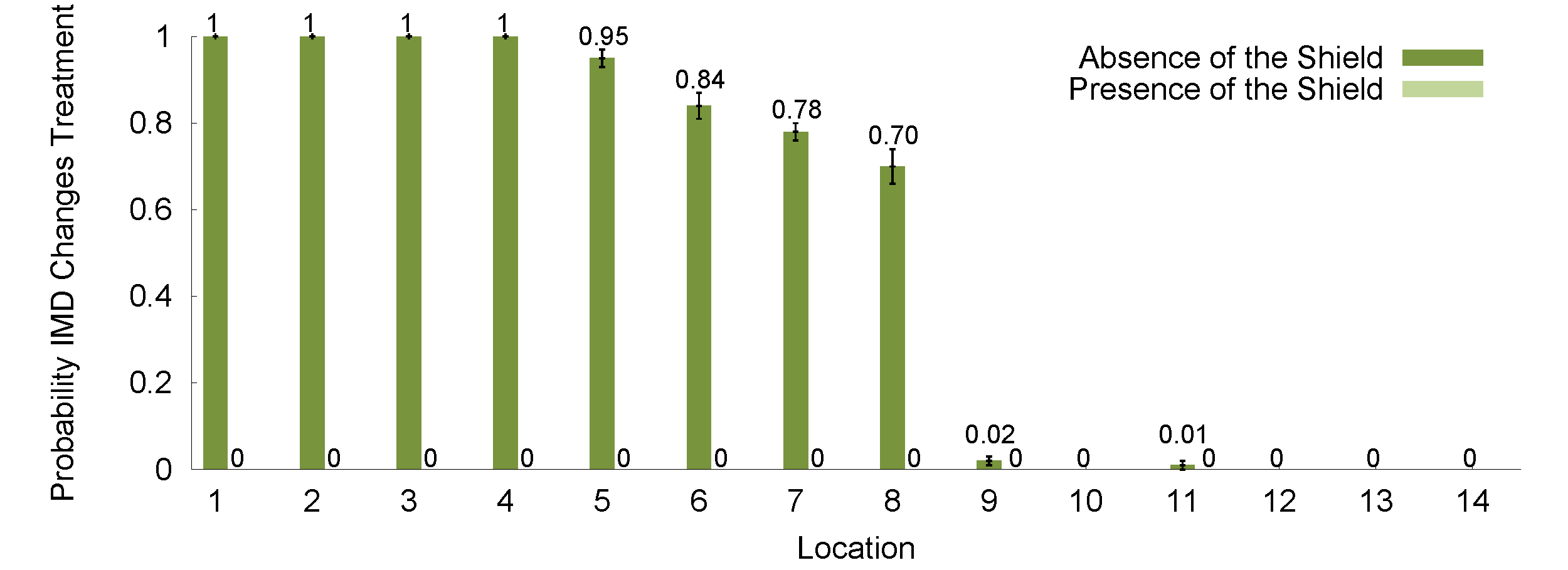
• When the shield is absent, the IMD replies to unauthorized commands,
even if the adversary is in a non-line-of-sight location
more than 14 m away, and uses a commercial device that operates
in the MICS band and adheres to the FCC power limit.
• When the shield is present and has the same transmit power as the
adversary, the IMD does not respond to unauthorized commands,
even when the adversary is only 20 cm away.
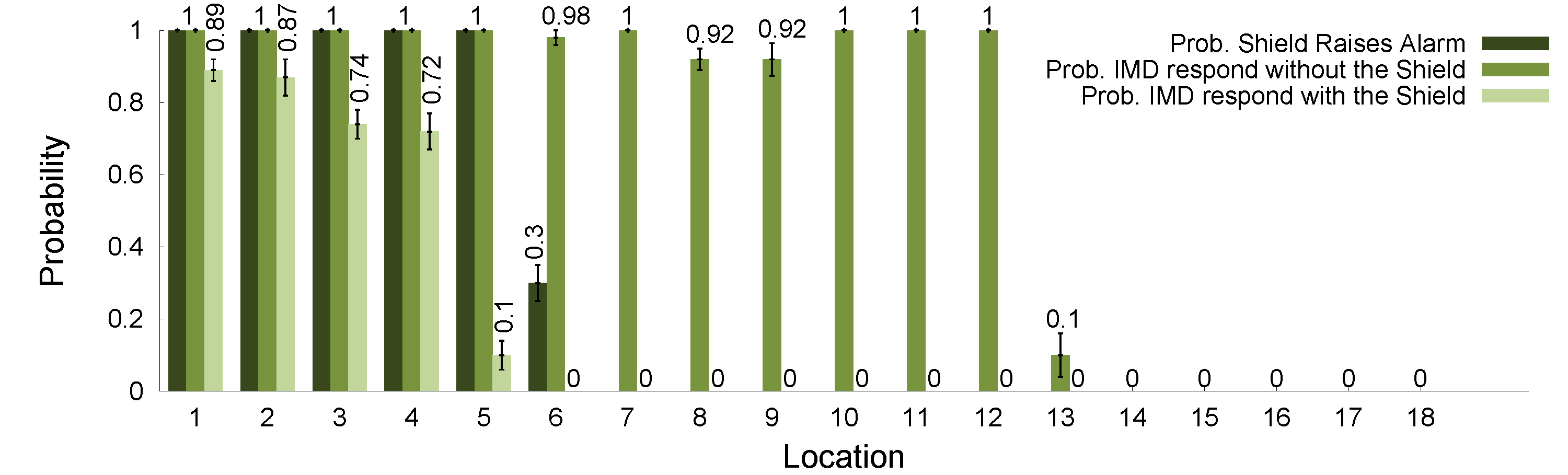
• When the shield is absent and an adversary with 100 times the
shield’s power transmits unauthorized commands, the IMD responds
from distances as large as 27 m.
• When the shield is
present the high-powered adversary’s attempts succeed
only from distances less than 5 m, and only in line-ofsight
locations. The shield always detects high-powered adversarial
transmissions and raises an alarm. We conclude that sufficiently
high-powered adversaries present an intrinsic limitation
to our physical-layer protection mechanism. However, the
shield’s presence reduces the adversary’s success range and informs
the patient, raising the bar for the adversary’s attempts.